Manterrò questo tutorial breve e facile da seguire. Con i comandi OpenSSL, quindi possiamo ottenere molte informazioni da un sito https come la data di scadenza del certificato, l'emittente dei certificati e l'impronta digitale e altre cose Iniziamo ora.
Quindi, come ottenere dati di informazioni SSL completi da un sito https
openssl s_client -servername NAME -connect HOST:PORT-servername è facoltativo ma puoi usarlo per inserire il nome fqdn
-connetti host:porta . se il sito Web e la porta nella maggior parte delle situazioni sono 443, altrimenti metti la vera porta SSL
Ottieni anche i dati completi del certificato con OpenSSL
openssl s_client -servername unixcop.com -connect unixcop.com:443
CONNECTED(00000004)
depth=2 C = US, O = Internet Security Research Group, CN = ISRG Root X1
verify return:1
depth=1 C = US, O = Let's Encrypt, CN = R3
verify return:1
depth=0 CN = unixcop.com
verify return:1
---
Certificate chain
0 s:CN = unixcop.com
i:C = US, O = Let's Encrypt, CN = R3
1 s:C = US, O = Let's Encrypt, CN = R3
i:C = US, O = Internet Security Research Group, CN = ISRG Root X1
2 s:C = US, O = Internet Security Research Group, CN = ISRG Root X1
i:O = Digital Signature Trust Co., CN = DST Root CA X3
---
Server certificate
-----BEGIN CERTIFICATE-----
MIIFLTCCBBWgAwIBAgISBFQRFmfTSdVTX55lc1IttlfZMA0GCSqGSIb3DQEBCwUA
MDIxCzAJBgNVBAYTAlVTMRYwFAYDVQQKEw1MZXQncyBFbmNyeXB0MQswCQYDVQQD
EwJSMzAeFw0yMTA4MjAxNDIwNTJaFw0yMTExMTgxNDIwNTFaMBYxFDASBgNVBAMT
C3VuaXhjb3AuY29tMIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEA0Mbt
LWf/Eu/1JzFoDSWKg/qFkOl5ByjIZ5EcGi8jv6EeDIToYNbgVHdcbSszigIyv6Z4
/CvZuxyAlOqBhxjKhtL4zuPFgLuE2UEX5dyiBP0MzuNR/xFXX/3iaJKoptuQTmJJ
FZ1fwWHsPWtGvI8ZGdBH8r0rPMvACcs0+SDDF3/tcpQg2tz3hxZwFTuWyQ8zQvui
XHtq724gjPGvr3huJ74Q6d/Uj/pgrHHFyke+f0FvlUnUdVT8UeTIlz7WOKP/cieh
NpJ+S7FyPaxuztuJqBwQwQtXHy8NNcZyzVMqOtGnODJG/k9WqrpvZgpig+b9ReQT
iV8XpJO7MeGESTB1cwIDAQABo4ICVzCCAlMwDgYDVR0PAQH/BAQDAgWgMB0GA1Ud
JQQWMBQGCCsGAQUFBwMBBggrBgEFBQcDAjAMBgNVHRMBAf8EAjAAMB0GA1UdDgQW
BBSWxY3A0mjbpTe02TPrp+y/vWkcaDAfBgNVHSMEGDAWgBQULrMXt1hWy65QCUDm
H6+dixTCxjBVBggrBgEFBQcBAQRJMEcwIQYIKwYBBQUHMAGGFWh0dHA6Ly9yMy5v
LmxlbmNyLm9yZzAiBggrBgEFBQcwAoYWaHR0cDovL3IzLmkubGVuY3Iub3JnLzAn
BgNVHREEIDAeggt1bml4Y29wLmNvbYIPd3d3LnVuaXhjb3AuY29tMEwGA1UdIARF
MEMwCAYGZ4EMAQIBMDcGCysGAQQBgt8TAQEBMCgwJgYIKwYBBQUHAgEWGmh0dHA6
Ly9jcHMubGV0c2VuY3J5cHQub3JnMIIBBAYKKwYBBAHWeQIEAgSB9QSB8gDwAHUA
RJRlLrDuzq/EQAfYqP4owNrmgr7YyzG1P9MzlrW2gagAAAF7ZCaLIwAABAMARjBE
AiAFljtSwllL7T20p2oOAKXiemCvk3mYURJLqULiEdI7VQIgVwzoGReeSFFPJB8N
urF+Q8npj/giaucw3q0dTbXHTSAAdwB9PvL4j/+IVWgkwsDKnlKJeSvFDngJfy5q
l2iZfiLw1wAAAXtkJosyAAAEAwBIMEYCIQDL4Cw/6iK8pWFlATSBdlkQtVj2hrKk
QDLZuw2wELXlmgIhAPRE9slgsqH8Bt5LlGAJ2CLeFQYxs79IZuuwxxMDFTRWMA0G
CSqGSIb3DQEBCwUAA4IBAQB5BTtp1BzuNCHEoi/S4ESt9O5gnu3KieMpWQ9ranH8
7XFgK+b4KNcy4r/H399u+auLhBxC4/+cR91Dh6hpTERhrcjENnWrTLgUrnSX/Kse
nsrFOUggjx12zB7hcC+iENixbFRjREDZOWZ9HOPEiaw6+GhFYEVRR9drpihamvQu
P0GBheT712z95yAc4BkiTUN5JBlj4D0f/zhIzpIPkJoYY+oxJ8qMmSUgD8wrtzVD
MqlcJWrQoZycLB7ZxICG9uqkCFoij+LaFaQsoIWElXMpsQ5Yo+AUkZeLF5R6HZE4
Q9CNy8wYRMsO1SYtMMmqI1jitdrVWsTacPcJhSjtPDFV
-----END CERTIFICATE-----
subject=CN = unixcop.com
issuer=C = US, O = Let's Encrypt, CN = R3
---
No client certificate CA names sent
Peer signing digest: SHA256
Peer signature type: RSA-PSS
Server Temp Key: X25519, 253 bits
---
SSL handshake has read 4674 bytes and written 408 bytes
Verification: OK
---
New, TLSv1.2, Cipher is ECDHE-RSA-CHACHA20-POLY1305
Server public key is 2048 bit
Secure Renegotiation IS supported
Compression: NONE
Expansion: NONE
No ALPN negotiated
SSL-Session:
Protocol : TLSv1.2
Cipher : ECDHE-RSA-CHACHA20-POLY1305
Session-ID: CFDB4E84054B0B5F580C96198CE25DAFE3BD7FE54DC92B03B6C4482D324D1D43
Session-ID-ctx:
Master-Key: 825683C91BB0D2EA44E38C57446D5B9896CFB7B23CD5E5F3CCD070C09A56E5B00655BC686D31E4954A7D889EF21D2083
PSK identity: None
PSK identity hint: None
SRP username: None
TLS session ticket lifetime hint: 86400 (seconds)
TLS session ticket:
0000 - 98 a5 75 00 cb 44 c0 4d-ce 6f c2 1e b1 b9 6e 48 ..u..D.M.o....nH
0010 - 25 69 11 0d 46 d0 e5 c5-e5 1e 1e 45 1d 06 8a cf %i..F......E....
0020 - 56 5c 4c 30 37 f6 7a a3-56 5d 5c 75 a0 d2 7f 71 V\L07.z.V]\u...q
0030 - 53 b1 f7 a1 41 3e 95 01-12 95 30 05 cc 30 a0 f1 S...A>....0..0..
0040 - 7e b7 44 14 3c c2 8e 77-66 48 bc a7 b1 f5 96 62 ~.D.<..wfH.....b
0050 - ce 1b 9c 35 e8 17 fc 61-4b 7b a3 60 d7 b8 bd 76 ...5...aK{.`...v
0060 - dc 54 71 95 3a 4d 7f 13-07 bd 4c 20 95 7a c5 a5 .Tq.:M....L .z..
0070 - 84 42 56 aa 7b 02 22 59-56 3a 11 3d 5f ee e5 1a .BV.{."YV:.=_...
0080 - 7d 80 c1 1a 7b 74 56 cd-89 cf 2e 7f 5a fd 2f 81 }...{tV.....Z./.
0090 - 0a 8e 14 88 14 be ae 4b-3d 03 83 49 d8 c9 a0 cc .......K=..I....
00a0 - ac 0b 07 ff 06 4e 8e cc-8b a4 48 b2 03 10 30 29 .....N....H...0)
00b0 - 56 9f f5 ca fa ca 80 75-a5 fd 61 1a 9a 2d 17 40 V......u..a..-.@
Start Time: 1633592990
Timeout : 7200 (sec)
Verify return code: 0 (ok)
Extended master secret: yes
---
closed
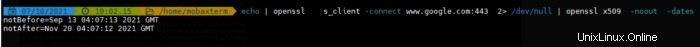
OpenSSL:verifica la data di scadenza del certificato SSL
Quindi esegui il comando per vedere la scadenza in un comando
echo| openssl s_client -connect www.google.com:443 2> /dev/null | openssl x509 -noout -dates
notBefore=Sep 13 04:07:13 2021 GMT
notAfter=Nov 20 04:07:12 2021 GMT
Trova l'emittente del certificato SSL
echo | openssl s_client -connect www.unixcop.com:443 2> /dev/null| openssl x509 -noout -issuer
Trova a chi è stato rilasciato il certificato SSL
echo| openssl s_client -connect www.unixcop.com:443 2> /dev/null | openssl x509 -noout -subject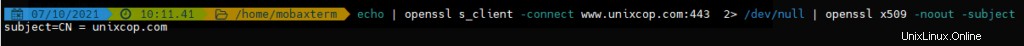
Supera le cose in una volta.
echo | openssl s_client -connect www.unixcop.com:443 2> /dev/null | openssl x509 -noout -issuer -subject -dates
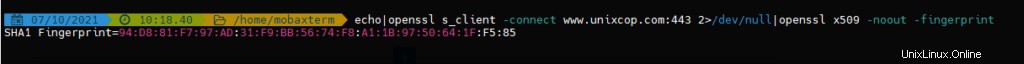
Mostra il SHA1 impronta digitale del certificato SSL
echo|openssl s_client -connect www.unixcop.com:443 2>/dev/null|openssl x509 -noout -fingerprint
SHA1 Fingerprint=94:D8:81:F7:97:AD:31:F9:BB:56:74:F8:A1:1B:97:50:64:1F:F5:85
Estrai tutte le informazioni dal certificato SSL
echo|openssl s_client -connect www.unixcop.com:443 2>/dev/null|openssl x509 -noout -text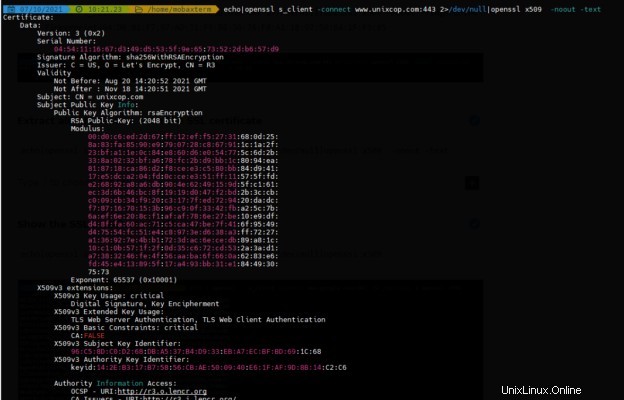
Mostra il certificato SSL stesso
echo|openssl s_client -connect www.unixcop.com:443 2>/dev/null|openssl x509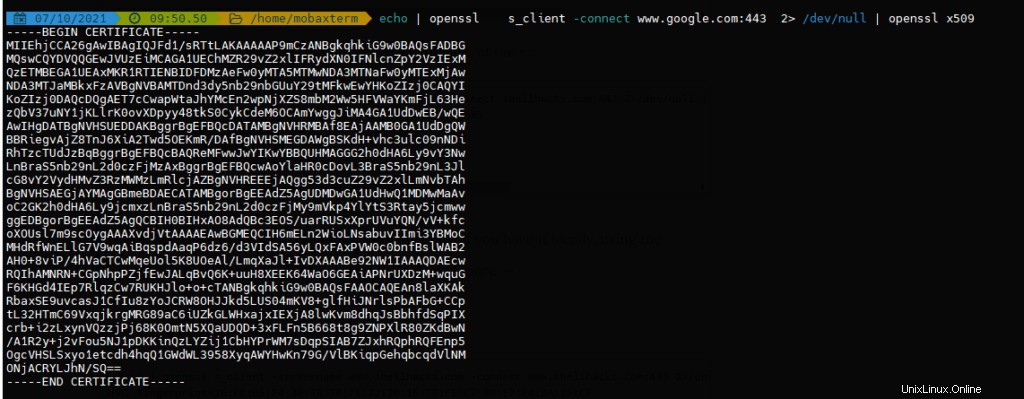
Oltre a qui ci sono le opzioni più utilizzate con openssl puoi vedere cose con man openssl
| Opzione | |
|---|---|
-text | Stampa il certificato in formato testo. |
-noout | Previene l'output della versione codificata della richiesta. |
-subject | Emette il nome. |
-issuer | Emette il nome dell'emittente. |
-dates | Stampa le date di inizio e di scadenza di un certificato. |
-fingerprint | Stampa il digest della versione codificata DER dell'intero certificato. |